Difference between revisions of "What the Security Is"
| (10 intermediate revisions by 2 users not shown) | |||
| Line 1: | Line 1: | ||
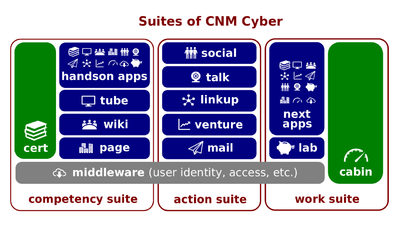
| − | [[File:Cnm-digital.png|400px|thumb|right|[[ | + | [[File:Cnm-digital.png|400px|thumb|right|[[CNMCyber suite]]s]][[What the Security Is]] (hereinafter, the ''Lectio'') is the [[lectio|lesson part]] of the '''[[Cyber Security Essentials]]''' [[lesson]] that introduces its participants to [[CNM Cabin]]. This ''lesson'' belongs to the [[Introduction to CNMCyber]] session of [[WorldOpp Orientation]]. |
| Line 6: | Line 6: | ||
===Script=== | ===Script=== | ||
| − | : | + | :[[CNMCyber Team]] strives to protect both the systems and data of [[CNMCyber]]. The ''Team'' distinguishes two branches of the security governance. |
| − | :The policy branch can be compared with the legislative branch of the government. This branch defines policies that serve as the law of the '' | + | :The policy branch can be compared with the legislative branch of the government. This branch defines policies that serve as the law of the ''CNMCyber'' land. |
:For instance, the [[privacy policy]] defines how sensitive [[user data]] can be collected and shared. The [[backup and recovery policy]] determines how the systems and data shall be protected from disaster losses. [[User access policy]] sets up what users can access what resources. [[Informational resource policy]] outlines the database management rules. Finally, [[human resource policy]] regulates the clearances and other practices towards the personnel that need to access the sensitive data because of their professional duties. | :For instance, the [[privacy policy]] defines how sensitive [[user data]] can be collected and shared. The [[backup and recovery policy]] determines how the systems and data shall be protected from disaster losses. [[User access policy]] sets up what users can access what resources. [[Informational resource policy]] outlines the database management rules. Finally, [[human resource policy]] regulates the clearances and other practices towards the personnel that need to access the sensitive data because of their professional duties. | ||
| Line 14: | Line 14: | ||
:The executive branch executes the policies and, especially, [[cyber-security]], which is protecting computers, data, and networks from potential attacks or unauthorized access. | :The executive branch executes the policies and, especially, [[cyber-security]], which is protecting computers, data, and networks from potential attacks or unauthorized access. | ||
| − | :To protect web operations of [[ | + | :To protect web operations of [[CNMCyber]], all of its [[website]] are secured with [[SSL certificate]]s. So, when you communicate with the ''Cyber'' over the [[Internet]], all of the communications are encrypted and practically impossible to hack. |
| − | : | + | :[[CNMCyber Team]] is constantly applying new security patches and is following security recommendations to protect its [[software system]]s from [[end-user application]]s and up to [[computing server]]s of the ''Cyber''. Specific information related to a particular system can be found in its [[product epic]] at [[CNM Wiki]]. |
:The access to the highest risk areas such as administrative projects of [[CNM Lab]] is protected by the [[public key infrastructure]] ([[public key infrastructure|PKI]]). This technology is the most secure from all that are available on the market. | :The access to the highest risk areas such as administrative projects of [[CNM Lab]] is protected by the [[public key infrastructure]] ([[public key infrastructure|PKI]]). This technology is the most secure from all that are available on the market. | ||
| Line 24: | Line 24: | ||
===Closing=== | ===Closing=== | ||
| − | :Would you be interested in working on [[cyber-security]] of [[ | + | :Would you be interested in working on [[cyber-security]] of [[CNMCyber]]? --Yes/No/I'm not sure |
'''[[User Data in Cyber]]''' is the successor [[lectio]]. | '''[[User Data in Cyber]]''' is the successor [[lectio]]. | ||
Latest revision as of 21:25, 29 October 2023
What the Security Is (hereinafter, the Lectio) is the lesson part of the Cyber Security Essentials lesson that introduces its participants to CNM Cabin. This lesson belongs to the Introduction to CNMCyber session of WorldOpp Orientation.
Content
The predecessor lectio is What Pipeline Is.
Script
- CNMCyber Team strives to protect both the systems and data of CNMCyber. The Team distinguishes two branches of the security governance.
- The policy branch can be compared with the legislative branch of the government. This branch defines policies that serve as the law of the CNMCyber land.
- For instance, the privacy policy defines how sensitive user data can be collected and shared. The backup and recovery policy determines how the systems and data shall be protected from disaster losses. User access policy sets up what users can access what resources. Informational resource policy outlines the database management rules. Finally, human resource policy regulates the clearances and other practices towards the personnel that need to access the sensitive data because of their professional duties.
- The executive branch executes the policies and, especially, cyber-security, which is protecting computers, data, and networks from potential attacks or unauthorized access.
- To protect web operations of CNMCyber, all of its website are secured with SSL certificates. So, when you communicate with the Cyber over the Internet, all of the communications are encrypted and practically impossible to hack.
- CNMCyber Team is constantly applying new security patches and is following security recommendations to protect its software systems from end-user applications and up to computing servers of the Cyber. Specific information related to a particular system can be found in its product epic at CNM Wiki.
- The access to the highest risk areas such as administrative projects of CNM Lab is protected by the public key infrastructure (PKI). This technology is the most secure from all that are available on the market.
Key terms
Closing
- Would you be interested in working on cyber-security of CNMCyber? --Yes/No/I'm not sure
User Data in Cyber is the successor lectio.